Ascertia, the leader in high-trust digital signatures and PKI solutions, is pleased to announce it has appointed Malek Bechlaghem as Managing Director for the MENA region.
Liaquat Khan

Recent Posts
Ascertia appoints Managing Director for MENA region
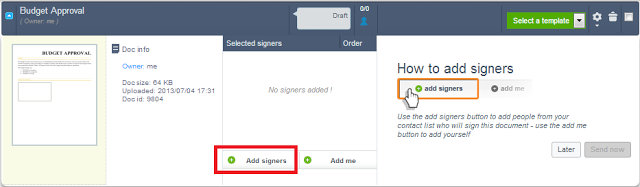
Understanding Bulk Signing
Digital signatures are supposed to make life easier, more secure and efficient. Certainly, when compared to signing with a pen and paper they are fantastic but imagine digitally signing hundreds, thousands or even millions of documents a day! Opening each document and signing with your mouse can be pretty tedious, even for tens of documents. There has to be a better way, and indeed there is, cue ‘bulk signing’.
Implementing the WHO SVCs using Ascertia PKI
In this blog, we discuss how Ascertia's Public Key Infrastructure (PKI) helps implement the World Health Organisation's (WHO) Smart Vaccination Certificates (SVCs).
It has become increasingly evident that to open up economies whilst ensuring the Covid-19 infection rate remains under control requires a mechanism whereby a person can present a document that proves they have received a vaccine.
Ascertia leading the way to an eIDAS-certified remote QSCD
In this blog, we discuss our efforts to secure an eIDAS-certified remote qualified signature creation device (QSCD).
We want to let you into a little secret. Since Sep 2017, Ascertia has been actively pursuing a Common Criteria EAL4+ certification of its ADSS Server “Signature Activation Module (SAM)” Appliance.
Interesting statistics from the 2017 Global PKI Trends Study
Last year’s IoT Solutions World Congress was an opportunity for the industry to focus on the increasing influence of the Internet of Things in PKI planning. We attended the event with our technology partner Thales e-Security, which has just published the 2017 Global PKI Trends report with the Ponemon Institute looking at trends across 11 countries.
International document regulations you need to know
In this blog, we discuss the international document regulations you need to know when making a digital transformation.
60+ countries have standards and legal frameworks for eSignatures and digital transactions. This list grows each year, which makes it challenging for international organisations to deliver compliant business processes.
Cloud signing: Advanced PKI digital signatures made easy
Ensuring secure, remote signing doesn't have to be challenging. In our latest blog, we're discussing cloud signing and the ease of using advanced PKI digital signatures.
OCSP Responder - the must have features!
This article discusses the features that should be on a highly desirable feature list when looking for an OCSP Responder product. Although the main focus of this topic is technical, there are commercial aspects that need consideration. These are summarised briefly at the end. The technical features explained here are all available and implemented in Ascertia ADSS OCSP Server, which is downloadable on trial basis.
Long-term signatures - the essential features
Does your business require digital signatures to be verifiable months, years or even decades later? In this blog, we discuss long-term signatures and what you should look for when choosing a provider.
Group and departmental level signing with SigningHub
In the real-world, it often doesn't matter who signs a document but rather do they have the sufficient group and departmental level authority to do this. That is the "identity" of the signer is not as important as the "authorisation". E.g. a Purchase Order typically requires an authorised member from the Procurement department to sign-off on it.